Safe(r) and (more) private browsing
This page was last modified on August 06, 2022
Our recommendations for a better web
This page is here to reflect our recommendations on web browsing. It applies to computers & tablets mostly. Smartphones come with many disadvantages regarding safe browsing and privacy and will not be handled here.
<TL;DR> We recommend using Mozilla Firefox web browser, with at least the following web extensions installed: uBlock Origin, Privacy Badger, Cookie Autodelete, Firefox Multi-Account Containers, and (to be absolutely complete) HTTPS Everywhere.
The selections below are our own, which doesn’t necessarily mean they are the best fitting for everyone. Some of those solutions may occasionally result in display issues, which is why it is important for you to learn and get familiar with those tools. It will all be worth it, if like us you care about the size of your footprints on the web.
Protecting yourself from adverts and trackers is not only good for you, but also for your carbon footprint ![]() . Think about it: by blocking all trackers and ads early on, your browser will not download them. That means you will not send multiple additional requests and require additional data transfer for downloading all those trackers and commercial that you could not care less about.
. Think about it: by blocking all trackers and ads early on, your browser will not download them. That means you will not send multiple additional requests and require additional data transfer for downloading all those trackers and commercial that you could not care less about.
For a typical free WordPress instance (with advertisements and trackers), enforcing those protection will scrape more than 1 MB (Megabyte) of data downloaded. This is huge! Here below is the same page (a free WordPress website) loaded with or without trackers and adverts blocking.
Without any blocking

With Firefox browser native blockers, plus uBlock Origin and Privacy Badger extensions
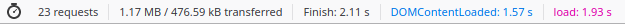
→ When protection is active, your browser makes 67 less requests, and downloads about 1.05 Megabytes less non pertinent data (i.e. 47.3% less in this case).
Browsers
Whichever browser you decide to use, the most critical thing is to keep it up-to-date to ensure you are protected against any known vulnerability.
The only web browser we thoroughly recommend is Firefox (download link), for the following reasons:
- Free and Open Source browser, available on all Operating systems
- Developed by the Mozilla foundation (not driven by profit)
- Fast, with a large catalogue of useful, privacy-friendly extensions (one-click install)
- They have been slowly moving towards a privacy by default design (accelerating since late of 2019)
Why not recommend Chromium or Brave, two Free and Open Source browsers also considered as good alternative to proprietary browsers?
Chromium is the FOSS version of Chrome, it is the rough material on which Google builds Chrome (adding proprietary and Google-only features). Brave is a fork of Chromium, with privacy-oriented extensions already installed and configured.
The answer is in the question ![]() . It’s because those are directly dependant from the choices of orientation that Google will make on its browser. Chrome browser is leading the browser adoption market by a long shot (about 60% in 2019. For latest metrics see the Wikipedia page), if everyone is using a Chromium-based browser, the features Google decides to push or retire with Chromium dictate how the web develops.
. It’s because those are directly dependant from the choices of orientation that Google will make on its browser. Chrome browser is leading the browser adoption market by a long shot (about 60% in 2019. For latest metrics see the Wikipedia page), if everyone is using a Chromium-based browser, the features Google decides to push or retire with Chromium dictate how the web develops.
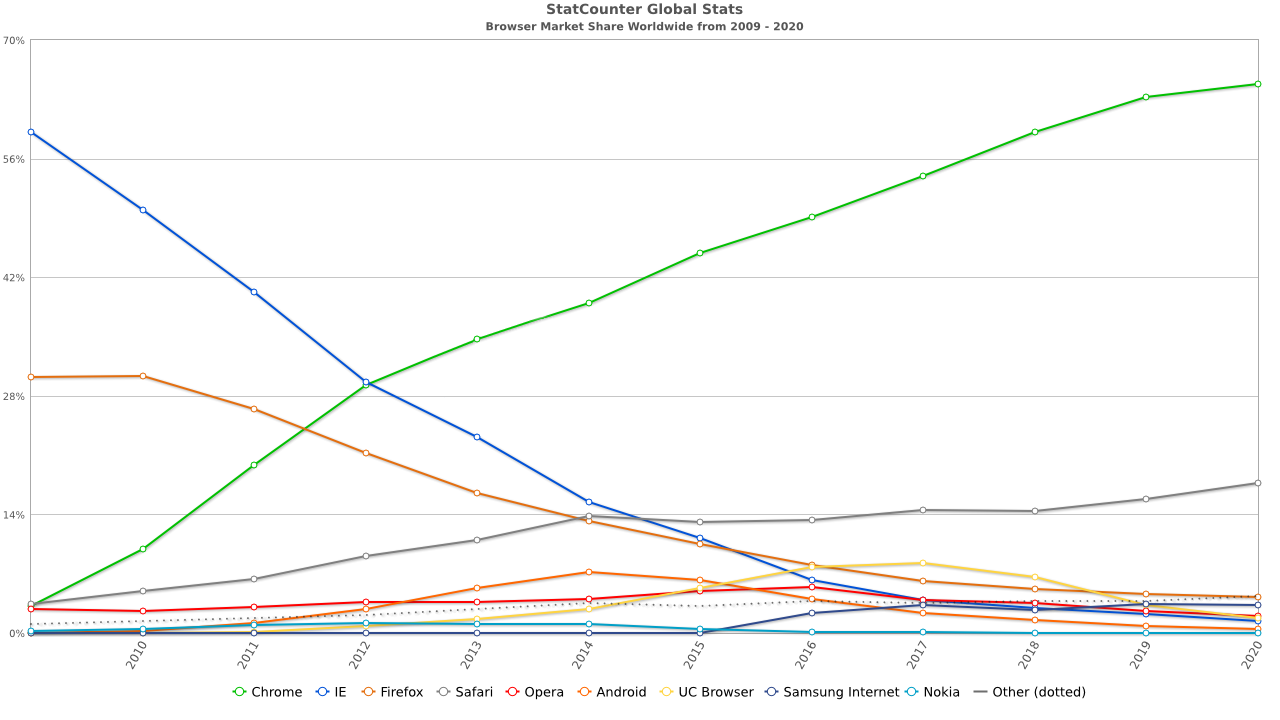
By StatCounter generated image, CC BY-SA 3.0, from Wikipedia
As of 2020, Firefox is pretty much the only alternative to a Chromium-based browser: Opera, Yandex, Vivaldi, and now Microsoft Edge, they all are Chromium-based! The other alternative being… Safari? ![]()
Web extensions for browser
Disclaimer
Browser extensions can make your experience significantly more enjoyable, or they can ruin it. An extension may not live to your expectancy, and having too many extensions installed and enabled is likely to slow down your browser. Also, some of the extensions we recommend can be quite blunt and have strong impact on the display of a web page. However, more often than not they are well worth the additional effort demanded on your part.
Extensions should always be installed from the browser official catalogue website. For Firefox, you can access them via Sandwich menu > Add-ons.
You should always be careful when installing a new extension. Carefully read the reviews, and confirm that the extension works as expected. If it’s not working the way you expected and/or after some time you realise that you are not using it, remove it.
Since we already chose Mozilla Firefox as the only good choice for a healthy Internet, we will focus on the extensions we recommend which are available there. We will start with what we consider the absolute minimum requirements, to optional extensions that can also prove useful for a safer browsing.
Absolute recommendations
All text descriptions below are extract from the extension’s page (as of 2020-01-18). All those extensions are of course Free and Open Source.
uBlock Origin
- What
An efficient blocker: easy on memory and CPU footprint, and yet can load and enforce thousands more filters than other popular blockers out there.
- Why
Because the Web is full of useless and annoying adverts, which your browser downloads and compute unnecessarily for you. All that energy goes to waste, and your browsing experience is worsened. If you should install only one extension, it would be the one.
- Usage
The big power button in the pop-up is to permanently disable/enable uBlock for the current web site. It applies to the current web site only, it is not a global power button.
Privacy Badger
- What
Privacy Badger automatically learns to block invisible trackers. Instead of keeping lists of what to block, Privacy Badger learns by watching which domains appear to be tracking you as you browse the Web.
Privacy Badger sends the Do Not Track signal with your browsing. If trackers ignore your wishes, your Badger will learn to block them. Privacy Badger starts blocking once it sees the same tracker on three different websites.
Besides automatic tracker blocking, Privacy Badger removes outgoing link click tracking on Facebook, Google and Twitter, with more privacy protections on the way.
- Why
Because trackers are clogging the Web and are huge contributors to that world-scale collection of data. Everything you browse online is potentially and often tracked. Privacy badger empowers you to progressively filter and clean up your browsing. We use it all the time. It’s also the extension that requires the most control over, as privacy badger will sometime block remote calls to legitimate website. We noticed this most notably when browsing other Peertube instances: on some website, peertube.nomagic.uk would be blocked by the badger. However since it’s super simple to allow a remote domain, it is not that much of an issue.
The Badger will soon help you reveal which website are clean and respectful of their visitors, and which don’t really give a damn.
- Example with The Guardian website:
Privacy Badger found 16 potential trackers on www.theguardian.com: ib.adnxs.com c.amazon-adsystem.com ad.crwdcntrl.net bcp.crwdcntrl.net tags.crwdcntrl.net googleads.g.doubleclick.net securepubads.g.doubleclick.net www.facebook.com www.google-analytics.com adservice.google.co.uk adservice.google.com cdn-gl.imrworldwide.com secure-au.imrworldwide.com secure-dcr.imrworldwide.com secure-gl.imrworldwide.com sb.scorecardresearch.comSo, when you browse on The Guardian without Privacy badger extension, you actually also reach out to Google, Amazon and Facebook (as of 2020-01-18, it will make little difference whether you are a subscriber or not).
Cookie AutoDelete
- What
Main Features:
- Auto Deletes Cookies from Closed Tabs
- Whitelist/ greylist Support for Cookies
- Easily Export/Import your whitelist/ greylist
- Clear All Cookies for a Domain
- Supports Manual Mode Cleaning from the pop-up
- Easily See the Number of Cookies for a site
- Support for Container Tabs (Firefox 53+ Only)
- Why
Cookies are small files saved on your device containing information about a specific website. They can improve your browsing experience when you reconnect to a website you visited earlier. The cookie will be read, and any settings that had been saved based on your preference during your last visit will be automatically loaded. It can be a language, a choice in a web form, anything really. The problem is, that some cookies do not actually bring anything to your experience, they are just a way to track you further. For example, Facebook cookie policy mentions:
Websites and apps provided by other companies that use the Facebook Products, including companies that incorporate the Facebook Technologies into their websites and apps. Facebook uses cookies and receives information when you visit those sites and apps, including device information and information about your activity, without any further action from you. This occurs whether or not you have a Facebook account or are logged in.
See the problem here? ![]()
This extension fix that. It’s one of the more complicated extensions, however it comes with a full documentation. It will be well worth your while if, like us, you want to ensure you are not constantly tracked while browsing the Web.
In a perfect world, such extension would not even exist because companies would be decent enough or compelled by law to respect your privacy. Yet, as of 2020, your browsing data is still for sale.
- Usage
This extension does not clean cookies automatically until you enable “Auto-clean”. This gives you the chance to add sites you often visit and trust to the whitelist before activating the “Auto-clean”.
- Add the sites you want to keep cookies in the whitelist (permanently) or greylist (until Browser restart)
- Toggle “Auto-clean” in the pop-up or “Automatic cleaning” in the settings
- Watch those unused cookies disappear :)
You must enable cookies in the browser as this extension will replace the internal cookie manager.
Firefox Multi-Account Containers
- What
Multi-Account Containers helps you keep all the parts of your online life contained in different tabs. Custom labels and colour-coded tabs help keep different activities — like online shopping, travel planning, or checking work email — separate. Under the hood, it separates website storage into tab-specific Containers. Cookies downloaded by one Container are not available to other Containers. With the Firefox Multi-Account Containers extension, you can…
Sign in to two different accounts on the same site (for example, you could sign in to work email and home email in two different Container tabs.
Keep different kinds of browsing far away from each other (for example, you might use one Container tab for managing your Checking Account and a different Container tab for searching for new songs by your favourite band) Avoid leaving social-network footprints all over the web (for example, you could use a Container tab for signing in to a social network, and use a different tab for visiting online news sites, keeping your social identity separate from tracking scripts on news sites)
- Why
It adds an extra layer of protection inside the browser. It’s easy to use (right-click → reopen in container) and is also super useful for signing to the same service with two different accounts (for example, we use it to sign on our Riot Web interface with our classic user using a Personal container, while also signing in as our administrator user using a Work container).
To be honest, it took us a long time before trying this extension out. But it was an immediate adoption, and we now use it all the time, and keep our important tabs tidily sorted in different containers.
HTTPS Everywhere
- What
Many sites on the web offer some limited support for encryption over HTTPS, but make it difficult to use. For instance, they may default to unencrypted HTTP, or fill encrypted pages with links that go back to the unencrypted site.
The HTTPS Everywhere extension fixes these problems by rewriting all requests to these sites to HTTPS.
- Why
Though there are a lot less than before, there are still some websites implementing both HTTP and HTTPS, without any automatic redirections or implementation of HSTS (HTTP Strict Transport Security: a web security policy mechanism published on the server which enforce communication from the client via a HTTPS only). This extension ensures for you that, for any domain in the list of the extension, your web browser will connect to that domain using an encrypted connection (HTTPS).
Not as useful as it used to be, because many most websites have adopted and are enforcing HTTPS, but can’t harm really and could still prove useful.
One step beyond
The extensions suggested below are for cybernauts who have a fair bit of technological background. They are considered less essentials, using them can break normal display (JS blocker) or return confusing results. If you wish to experiment, tread carefully and don’t hesitate to get in touch on the Fediverse (user @contact@social.nomagic.uk) if you have any questions, we’ll do what we can to help.
Javascript Toggle On and Off
- What
JavaScript Toggle On and Off add-on brings a bulletproof method to disable JavaScript execution in both standard and private modes. Note that after installation JavaScript execution is enabled, you need to click the toolbar button to disable the execution.
- Why
Blocking Javascript is a extremely efficient way to block trackers. However Javascript is also used for nice things, like adding interaction and automatic refresh on web pages. For example, if you disable Javascript on www.nomagic.uk, you would lost the following functions:
- Search page
- The coloured status in the footer of each page
- The ability to use our Fediverse social share button at the bottom of our posts
So this is why we recommend to only disable Javascript for very specific websites. Usually, disabling Javascript is done as an attempt to work around some nasty/idiotic implementations, like preventing you to right click on a web page. Other than specific use cases, Firefox itself (from version +70) as well as UBlock Origin, Privacy Badger and Cookie Autodelete should already give you a reasonable level of protection.
FlagFox
- What
Flagfox is an extension that displays a flag icon indicating the current web server’s physical location. Knowing where you’re connected to adds an extra layer of awareness to your browsing and can be useful to indicate the native languages and legal jurisdictions that may apply. Additional information can be obtained via a multitude of external lookups and users can add their own custom actions. All actions can be added to the flag icon’s context menu and set to icon click or keyboard shortcuts for quick access.
Clicking the flag icon loads our default action, Geotool, which gives a detailed map showing the city the server is in and other useful information such as its local time and ISP.
The privacy policy of the extension explains that no data is sent anywhere while using the add-on. It also mentions that when clicking on the flag and reaching out the GeoTool portal:
Flagfox sends the current server’s host name and IP address in the URL to be used as the basis to look up this additional information. Geotool is also sent version information for your current Flagfox install using a cookie. This information cannot be used to track anyone, as all people using the same version of Flagfox will use the same cookie to identify their same Flagfox version.
- Why
This extension displays where a web server is likely to be located. So typically, if you live in the UK but see that when connecting to your Banking website you get a US flag, you would want to double check which URL you are connecting to, as well as its TLS certificate, and the DNSSEC status of the connection, as this would look a lot like a phishing attempt.
This may be a bad example, as some banks actually host their customer website outside of the country of origin. You are free to accept that of course, it’s your money after all ![]() .
.
As you can see, it is possible to go quite deep into verifying the legitimacy of a website. Ensuring that you connect to the right server is probably the most important rule of safe browsing. Nowadays phishing attempts reproduce the exact look and feel of the website they are copying so that you give out your information “wilfully”. Service providers who care about trust should implement additional mechanism used to validate (or invalidate) the legitimacy of a sensitive website.
Days of the future past
DNSSEC, the underdog
DNSSEC adds another layer of legitimacy check when connecting to a remote server. Unfortunately, the adoption of DNSSEC has been very low over the years, with still no native support of any kind from any browser. Yet, a widespread adoption on DNSSEC (both servers and clients) would prevent fraudulent activity like issuance of fraudulent certificates to be successful (last known case was in 2015).
Maybe the spreading use of DoH (DNS over HTTPS) and DoT (DNS over TLS) will help getting some renewed attention to DNSSEC? We can only hope so!
At Nomagic, we do implement DNSSEC. So, we’ll already be ready when a shiny DNSSEC extension comes out! ![]()
Firefox browser icon licensed under MPL2
Privacy Badger icon licensed under CC BY 3.0 us
